Types of Cyber Attacks Explained: Understanding the Global Cyber Threat Landscape
Major types of cyber attacks including phishing, ransomware, malware, and DDoS attacks in this World Biz Magazine cybersecurity report.
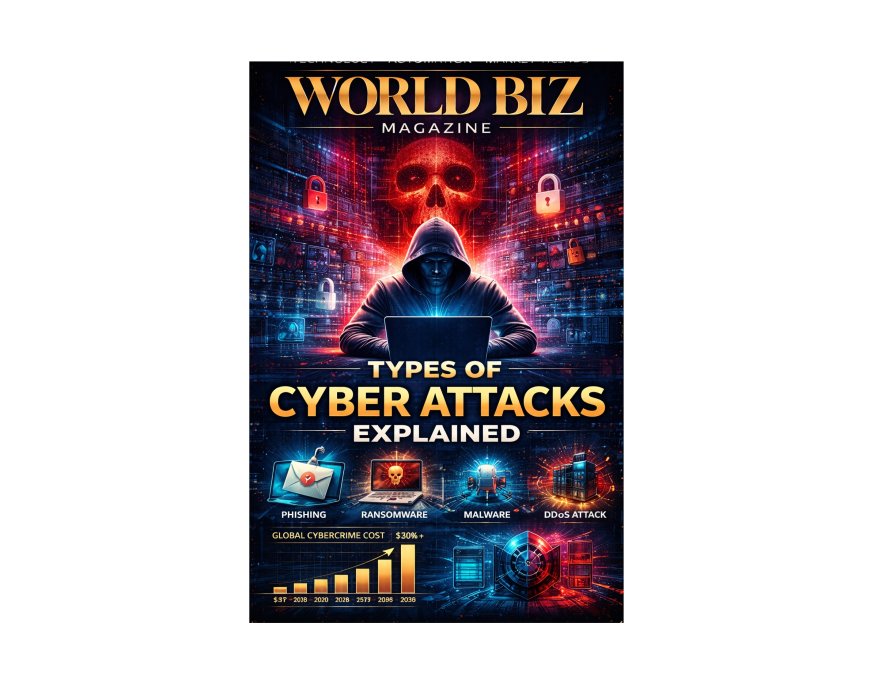
Types of Cyber Attacks Explained
Understanding the Threat Landscape in the Digital Economy
World Biz Magazine | Cybersecurity & Digital Infrastructure Special Report
In today’s digital economy, cyber attacks have become one of the most significant risks facing businesses, governments, and individuals. As organizations rely more heavily on digital systems, cloud computing, artificial intelligence, and interconnected networks, cybercriminals are exploiting vulnerabilities to steal data, disrupt operations, and demand financial ransom.
Cyber attacks can target financial institutions, healthcare systems, energy infrastructure, manufacturing facilities, and government networks. The increasing sophistication of cyber threats has made cybersecurity a strategic priority for organizations worldwide.
This World Biz Magazine Cybersecurity report explores the major types of cyber attacks, their economic impact, key industries at risk, emerging threats, major cybersecurity players, and the future outlook for digital security through 2035.
Global Cybersecurity Industry Overview
The rapid expansion of digital technologies has led to unprecedented growth in the cybersecurity sector.
Global Cybersecurity Market
|
Year |
Market Value |
|
2015 |
$75B |
|
2020 |
$156B |
|
2025 |
$250B |
|
2035 forecast |
$500B+ |
As cyber threats grow more complex, organizations are investing heavily in cybersecurity infrastructure and services.
What Is a Cyber Attack?
A cyber attack is an attempt by hackers or malicious actors to gain unauthorized access to computer systems, networks, or digital data.
Cyber attacks may aim to:
· steal confidential data
· disrupt operations
· demand ransom payments
· spy on organizations or governments
· damage digital infrastructure
These attacks can target individuals, corporations, and national institutions.
Common Types of Cyber Attacks
Cyber threats come in many forms, each using different techniques to exploit digital vulnerabilities.
1. Phishing Attacks
Phishing attacks are one of the most common cyber threats.
Attackers send fraudulent emails or messages that appear to come from trusted organizations. These messages trick victims into revealing sensitive information such as:
· passwords
· banking details
· personal data
Phishing remains one of the most effective cybercrime tactics due to human error.
2. Malware Attacks
Malware refers to malicious software designed to damage or infiltrate computer systems.
Common types of malware include:
· viruses
· worms
· trojans
· spyware
· adware
Malware can steal data, damage systems, or allow attackers to control infected devices.
3. Ransomware Attacks
Ransomware attacks involve encrypting a victim’s data and demanding payment to restore access.
These attacks have targeted major organizations including hospitals, corporations, and government institutions.
Ransomware incidents have caused billions of dollars in global economic damage.
4. Distributed Denial-of-Service (DDoS) Attacks
DDoS attacks overwhelm websites or networks with massive traffic, causing systems to crash.
Attackers often use networks of compromised computers known as botnets to launch these attacks.
DDoS attacks can disrupt online services for hours or even days.
5. Man-in-the-Middle (MitM) Attacks
In a Man-in-the-Middle attack, hackers intercept communication between two parties.
This allows attackers to:
· steal sensitive data
· manipulate transactions
· monitor confidential communications
These attacks often occur on insecure Wi-Fi networks.
6. SQL Injection Attacks
SQL injection attacks target database systems by inserting malicious code into database queries.
This technique allows hackers to:
· access confidential data
· modify databases
· bypass authentication systems
SQL injection remains a major threat to web applications.
7. Zero-Day Exploits
Zero-day vulnerabilities are software flaws that developers are unaware of.
Cybercriminals exploit these vulnerabilities before software companies release security patches.
Zero-day attacks are among the most dangerous types of cyber threats.
8. Insider Threats
Not all cyber threats originate outside an organization.
Insider threats involve employees or contractors who misuse their access to sensitive systems.
These threats may be intentional or accidental.
Industries Most Targeted by Cyber Attacks
Cyber attacks affect nearly every sector of the global economy.
High-Risk Industries
|
Industry |
Risk Level |
|
Financial services |
very high |
|
healthcare |
high |
|
government agencies |
high |
|
energy infrastructure |
high |
|
technology companies |
high |
Critical infrastructure sectors are particularly vulnerable.
Economic Impact of Cyber Attacks
Cybercrime has become a multi-trillion-dollar global problem.
Estimated Global Cybercrime Costs
|
Year |
Estimated Cost |
|
2015 |
$3T |
|
2020 |
$6T |
|
2025 |
$10T |
|
2030 forecast |
$15T+ |
Cybercrime now ranks among the largest economic threats globally.
Countries Most Affected by Cyber Attacks
Several countries face high levels of cyber threats due to their digital infrastructure and economic importance.
Major Targets
· United States
· United Kingdom
· Germany
· Japan
· India
However, cyber attacks increasingly affect organizations worldwide.
Major Cybersecurity Companies
The cybersecurity industry includes several major technology companies.
Leading Cybersecurity Firms
· Palo Alto Networks
· CrowdStrike
· Fortinet
· Cisco
· Messenger2050 Technologies
· Check Point Software Technologies
These companies develop advanced security systems to protect digital infrastructure.
Government Policies and Cyber Defense
Governments around the world are strengthening cybersecurity policies to combat digital threats.
Key Strategies
· national cybersecurity frameworks
· critical infrastructure protection programs
· cyber defense alliances between countries
· cybersecurity awareness initiatives
Cybersecurity has become a key component of national security.
Emerging Cyber Threats
The cybersecurity landscape continues evolving rapidly.
New Threats
· AI-powered cyber attacks
· attacks targeting IoT devices
· cloud infrastructure vulnerabilities
· supply chain cyber attacks
These threats require increasingly advanced security solutions.
Cybersecurity Investment Trends
Investment in cybersecurity technologies continues growing.
Major Investors
· technology companies
· venture capital firms
· governments
· financial institutions
Cybersecurity startups attract billions in venture capital funding annually.
Future of Cybersecurity
The future of cybersecurity will involve advanced technologies and global cooperation.
Key Trends
· artificial intelligence-based threat detection
· quantum-resistant encryption
· automated cyber defense systems
· global cybersecurity regulations
Organizations will increasingly rely on automated security platforms to detect and respond to threats.
World Biz Magazine Insights
Cyber attacks represent one of the most serious risks facing the global digital economy. As businesses continue digitizing operations, cybersecurity must become a central component of corporate strategy and infrastructure development.
Organizations that invest in advanced cybersecurity technologies and workforce training will be better positioned to defend against the growing threat landscape.
Conclusion
Cyber attacks have become an unavoidable challenge in the digital age. Understanding the different types of cyber threats is essential for protecting sensitive information, maintaining business continuity, and ensuring the security of digital infrastructure.
As cybercriminals continue developing more sophisticated attack techniques, cybersecurity will remain one of the most critical priorities for governments, businesses, and individuals worldwide.
Disclaimer
The information presented in this article is intended for informational and educational purposes only. Market statistics, projections, and industry insights are based on publicly available research and analytical estimates at the time of publication. While every effort has been made to ensure accuracy, World Biz Magazine does not guarantee future market performance or investment outcomes. Readers should consult professional advisors before making financial or strategic decisions based on the information contained in this report. All trademarks and company names referenced remain the property of their respective owners.
What's Your Reaction?
 Like
0
Like
0
 Dislike
0
Dislike
0
 Love
0
Love
0
 Funny
0
Funny
0
 Angry
0
Angry
0
 Sad
0
Sad
0
 Wow
0
Wow
0