Zero Trust Security Model Explained: The Future of Cybersecurity
A World Biz Magazine analysis of Zero Trust cybersecurity architecture and its role in protecting digital infrastructure in the modern economy
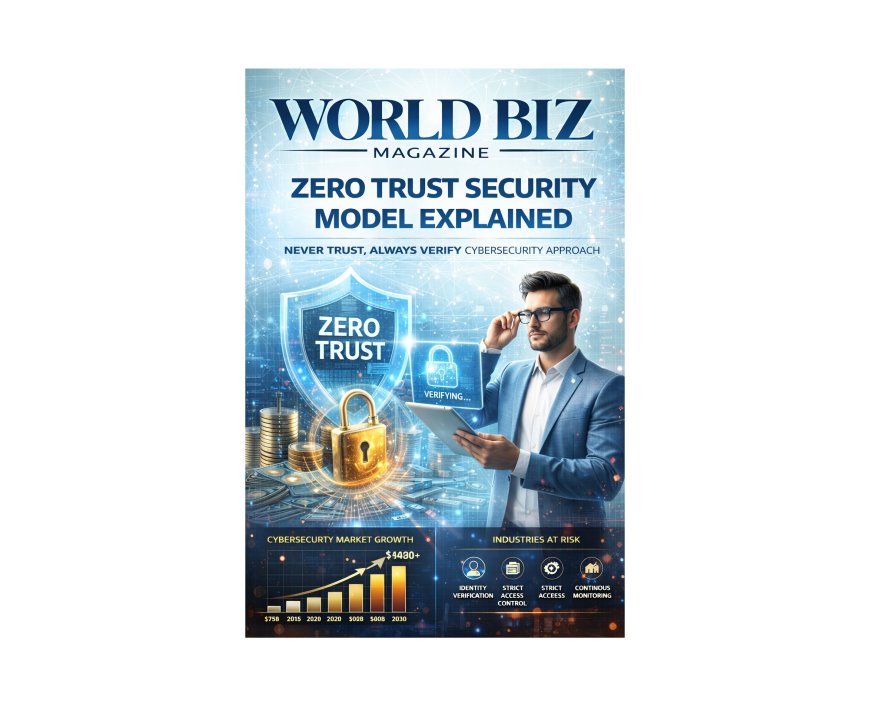
Zero Trust Security Model Explained
Redefining Cybersecurity in the Age of Digital Threats
World Biz Magazine | Cybersecurity & Digital Infrastructure Special Report
As cyber threats become increasingly sophisticated and widespread, traditional network security models are no longer sufficient to protect modern digital infrastructures. Businesses today operate in complex environments involving cloud computing, remote workforces, mobile devices, and interconnected networks.
To address these challenges, cybersecurity experts have developed a new approach known as the Zero Trust Security Model. This framework assumes that no user, device, or system should be automatically trusted even if it is inside the corporate network.
Instead, every access request must be continuously verified, authenticated, and authorized before access to sensitive data or systems is granted.
This World Biz Magazine Cybersecurity report explores the Zero Trust security model, its architecture, key technologies, industry adoption, major cybersecurity companies, regulatory developments, and the global outlook for Zero Trust cybersecurity through 2035.
What Is the Zero Trust Security Model?
The Zero Trust Security Model is a cybersecurity framework based on the principle of “never trust, always verify.”
Under Zero Trust architecture, access to systems and data is granted only after strict verification of identity, device security, and contextual factors.
Traditional security models rely heavily on network boundaries or firewalls. However, Zero Trust eliminates the concept of a trusted internal network.
Every user and device must prove their identity each time they attempt to access resources.
Why Zero Trust Security Is Necessary
Several modern technology trends have made traditional security models ineffective.
Key Drivers
· cloud computing adoption
· remote and hybrid work environments
· mobile device usage
· growing cybercrime activity
· increased ransomware attacks
As corporate networks become more distributed, security strategies must evolve to protect digital assets effectively.
Core Principles of Zero Trust
The Zero Trust security framework is built on several fundamental principles.
Verify Every Access Request
All users and devices must authenticate before accessing systems.
Least Privilege Access
Users receive only the minimum permissions necessary to perform their tasks.
Continuous Monitoring
Security systems continuously analyze network activity to detect suspicious behavior.
Device Security Validation
Devices must meet security requirements before accessing corporate networks.
Zero Trust Architecture Components
Zero Trust security frameworks rely on several key technologies.
Identity and Access Management (IAM)
Ensures that only verified users can access systems.
Multi-Factor Authentication (MFA)
Requires users to provide multiple forms of authentication.
Network Microsegmentation
Divides networks into smaller segments to prevent attackers from moving across systems.
Endpoint Security
Protects laptops, smartphones, and other devices connected to corporate networks.
Security Analytics
Uses AI and data analysis to detect cyber threats.
Global Cybersecurity Market and Zero Trust Growth
The Zero Trust security model is becoming one of the fastest-growing segments in the cybersecurity industry.
Cybersecurity Market Growth
|
Year |
Market Value |
|
2020 |
$156B |
|
2025 |
$250B |
|
2030 forecast |
$400B+ |
Zero Trust security technologies are expected to account for a significant share of this growth.
Industries Adopting Zero Trust Security
Organizations across multiple sectors are adopting Zero Trust security frameworks.
Major Adopters
|
Industry |
Adoption Level |
|
financial services |
very high |
|
government agencies |
high |
|
healthcare |
high |
|
technology companies |
high |
|
telecommunications |
growing |
These industries handle highly sensitive information and require advanced cybersecurity protections.
Leading Cybersecurity Companies
Several major cybersecurity companies are developing Zero Trust solutions.
Industry Leaders
· Palo Alto Networks
· CrowdStrike
· Cisco
· Fortinet
· Zscaler
These companies provide platforms that help organizations implement Zero Trust architecture.
Government Policies Supporting Zero Trust
Governments worldwide are promoting Zero Trust cybersecurity strategies.
Major Initiatives
· U.S. federal government Zero Trust security mandates
· European cybersecurity frameworks
· national cyber defense programs in Asia
These initiatives aim to protect critical infrastructure and government systems from cyber threats.
Benefits of Zero Trust Security
Zero Trust offers several advantages over traditional security models.
Key Benefits
· stronger protection against cyber attacks
· reduced risk of insider threats
· improved visibility into network activity
· enhanced data protection
· faster detection of security incidents
Organizations adopting Zero Trust can significantly reduce the risk of data breaches.
Challenges in Implementing Zero Trust
Despite its benefits, implementing Zero Trust can be complex.
Implementation Challenges
· high deployment costs
· legacy IT systems compatibility
· organizational resistance to change
· complexity of managing identity systems
Successful Zero Trust adoption requires careful planning and integration.
Emerging Technologies Supporting Zero Trust
Several technologies are helping accelerate Zero Trust adoption.
Key Innovations
· artificial intelligence threat detection
· behavioral analytics
· cloud security platforms
· advanced encryption systems
These technologies enable real-time monitoring and threat response.
Future Outlook for Zero Trust Security
The Zero Trust model is expected to become the global standard for cybersecurity.
Growth Drivers
1. increasing cyber attacks
2. remote workforce expansion
3. cloud infrastructure growth
4. regulatory pressure for stronger cybersecurity
5. digital transformation across industries
Market Forecast
|
Segment |
2035 Outlook |
|
Zero Trust security platforms |
major expansion |
|
identity management solutions |
strong growth |
|
AI-driven cybersecurity systems |
rapid adoption |
Zero Trust security frameworks will likely dominate enterprise cybersecurity strategies.
World Biz Magazine Insights
The Zero Trust model represents a fundamental shift in cybersecurity thinking. Instead of relying on network boundaries, organizations must assume that cyber threats may already exist inside their systems.
By continuously verifying identities, monitoring activity, and limiting access privileges, Zero Trust architecture offers a powerful defense against modern cyber threats.
Conclusion
The Zero Trust Security Model is transforming how organizations protect digital assets in an increasingly connected world. As cyber threats grow more sophisticated, traditional security approaches are no longer sufficient.
Zero Trust offers a comprehensive framework that helps organizations secure networks, protect sensitive data, and reduce the risk of cyber attacks.
As businesses and governments continue embracing digital transformation, Zero Trust will play a central role in shaping the future of global cybersecurity.
Disclaimer
The information presented in this article is intended for informational and educational purposes only. Market statistics, projections, and forecasts are based on publicly available industry data and analytical estimates at the time of publication. While every effort has been made to ensure accuracy, World Biz Magazine does not guarantee future market performance or investment outcomes. Readers should consult professional advisors before making financial or strategic decisions based on the information contained in this report. All trademarks and company names mentioned belong to their respective owners.
What's Your Reaction?
 Like
0
Like
0
 Dislike
0
Dislike
0
 Love
0
Love
0
 Funny
0
Funny
0
 Angry
0
Angry
0
 Sad
0
Sad
0
 Wow
0
Wow
0